
Microsoft Visio threat modeling workflow
Microsoft Visio threat modeling workflow
Prerequisites
You're expected to have followed the previous step by step tutorial (Threat modeling workflow for AWS Cloudformation architectures using IriusRisk) to configure the IriusRisk API and the Postman API client so that they can speak to each other in a seamless way.
You should use the latest version of the IriusRisk API documentation published at SwaggerHub (1.16.0 at the current time).
Visio defined architecture example
As we’ve talking about in past articles, architecture diagrams are very useful to show you a bird’s-eye view of how an application or system is organized for software components. Microsoft Visio is a very well known diagrammatic tool by Microsoft Windows that offers templates and symbols for different kinds of visual content like organizational charts, network diagrams, flowcharts, floor plans, etc.
Visio has many inbuilt AWS shapes and stencils that can be placed and arranged on the canvas. Follow this step by step tutorial to import a Visio AWS Visio architecture into IriusRisk as a hands-on example.
You can find the AWS Visio architecture we’ll be using along with this article in the following location:
https://github.com/iriusrisk/startleft/blob/main/examples/visio/aws-with-tz-and-vpc.vsdx

How to use Postman to automatically create a threat model in IriusRisk from a Visio diagram
Now we can use Postman to upload this Visio template to automatically create a new threat model in IriusRisk for this example architecture. In order to do this, you can follow the next three steps:
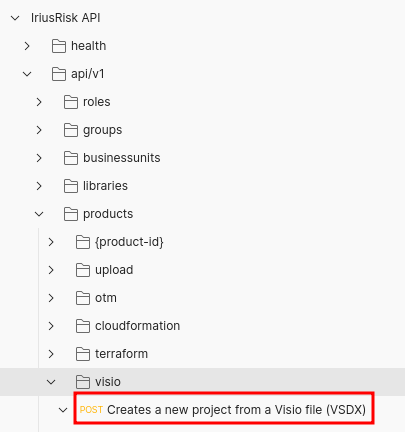
Step 1: Select the Visio API endpoint
First, we need to click on the Visio endpoint (POST/api/v1/products/visio) in the Postman collection navigation tree. This API endpoint is intended to create a new IriusRisk project from a Visio file (VSDX):
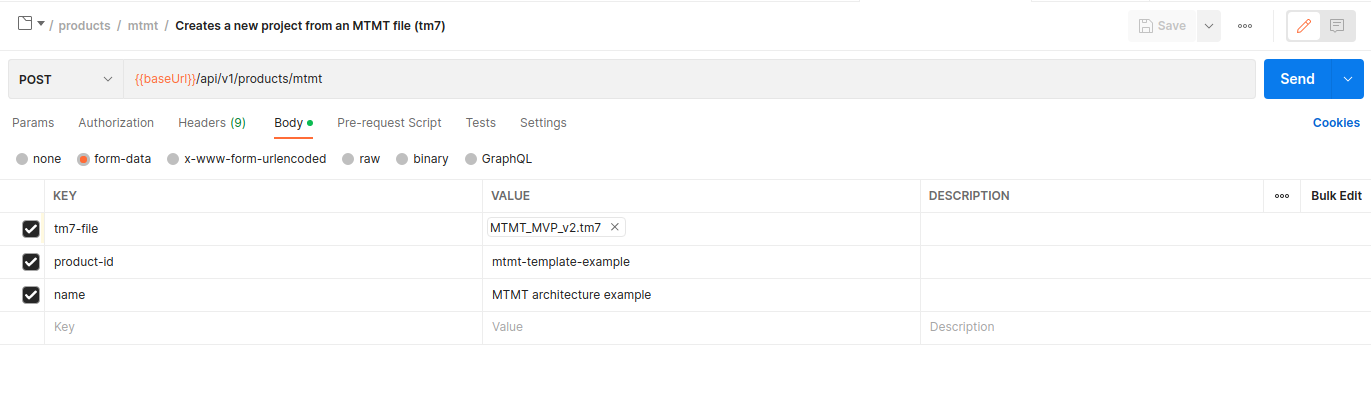
A new tab opens. You can set the necessary parameters for this HTTP request in the Body submenu, as can be seen in the following figure:

Step 2: Set the API request parameters
Now, we'll set the HTTP body parameters:
- vsdx-file: (Required) File that contains the Visio file.
- product-id: (Required) Id of the new project in IriusRisk.
- name: (Required) Name of the new project in IriusRisk.
- mapping-file: (Optional) File that contains the mapping between generic Visio shapes and IriusRisk components.
To keep this importation template simple, we'll use the default mapping between Visio and IriusRisk components. This way, we won't need to specify the mapping-file and we can deselect this parameter in the Postman checkbox. One example of this mapping file could be found in the StartLeft Github repository. Right now, this default mapping file supports some basic AWS components. However, we’ll continue expanding this default mapping file in the next IriusRisk releases, but if you need to customize this mapping to fit your specific requirements, you can provide your own YAML mapping file to the API using the mapping-file variable.
The next step, is to select our simple example for a Visio template (aws-with-tz-and-vpc.vsdx) as the value of the vsdx-file parameter. Then we set the product-id and name parameters that will be used to create a new project in IriusRisk. Finally, we click on the "Save" button to persist this configuration. This is how it looks in the HTTP POST request configuration right now:
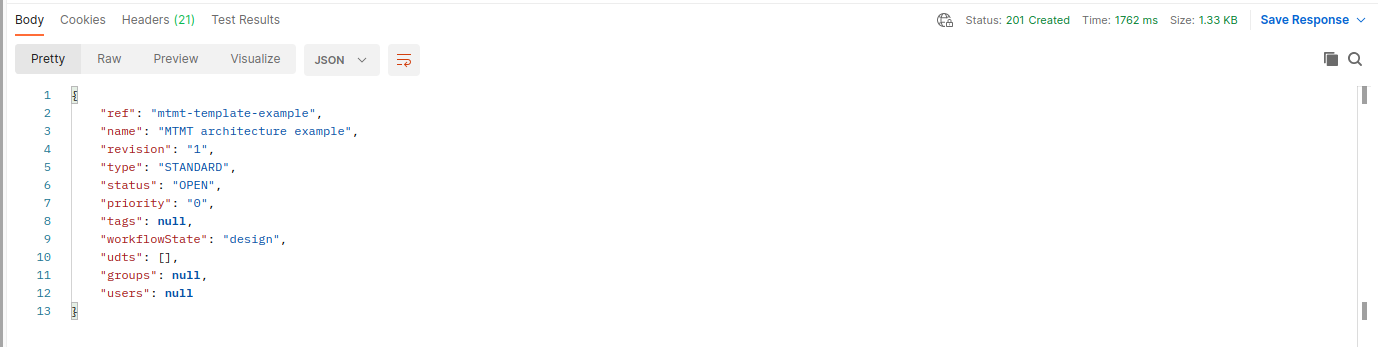
Step 3: Send the API request
We are ready to click on the "Send" button to actually send the HTTP request and create the new IriusRisk project from our Visio template. If everything goes well, we'll receive a 201 HTTP code from the IriusRisk server and the following Body response with some basic information about the newly created project:
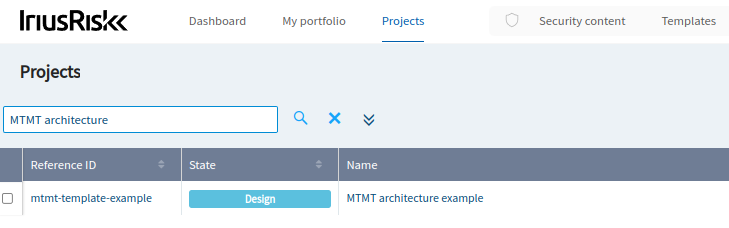
Review the generated threat model in IriusRisk
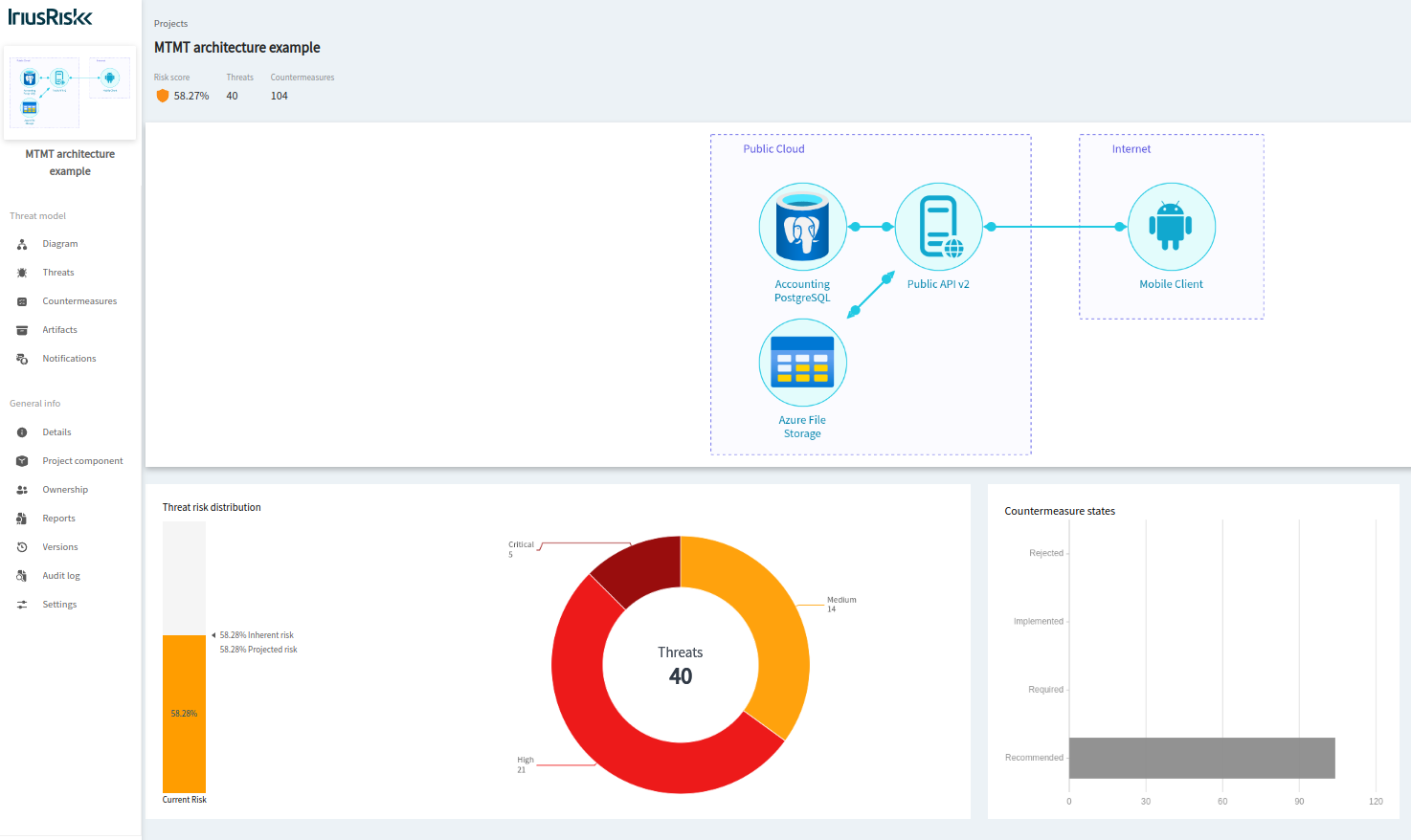
If we log in in the IriusRisk UI, we'll see that a new threat model was automatically created based on our Visio template architecture:
This is how it looks in the project home page as a visual summary of some of the main security metrics involved for this threat model:
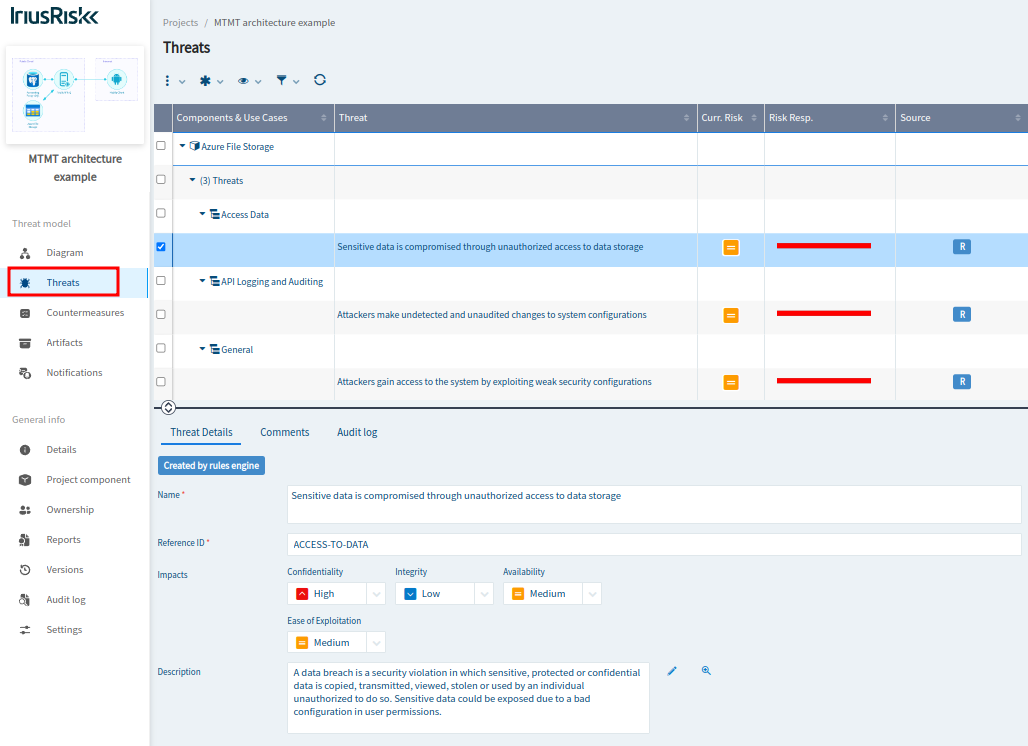
To see the relevant threats and countermeasures for this simple architecture, you can go to the "Threats" section on the left pane:
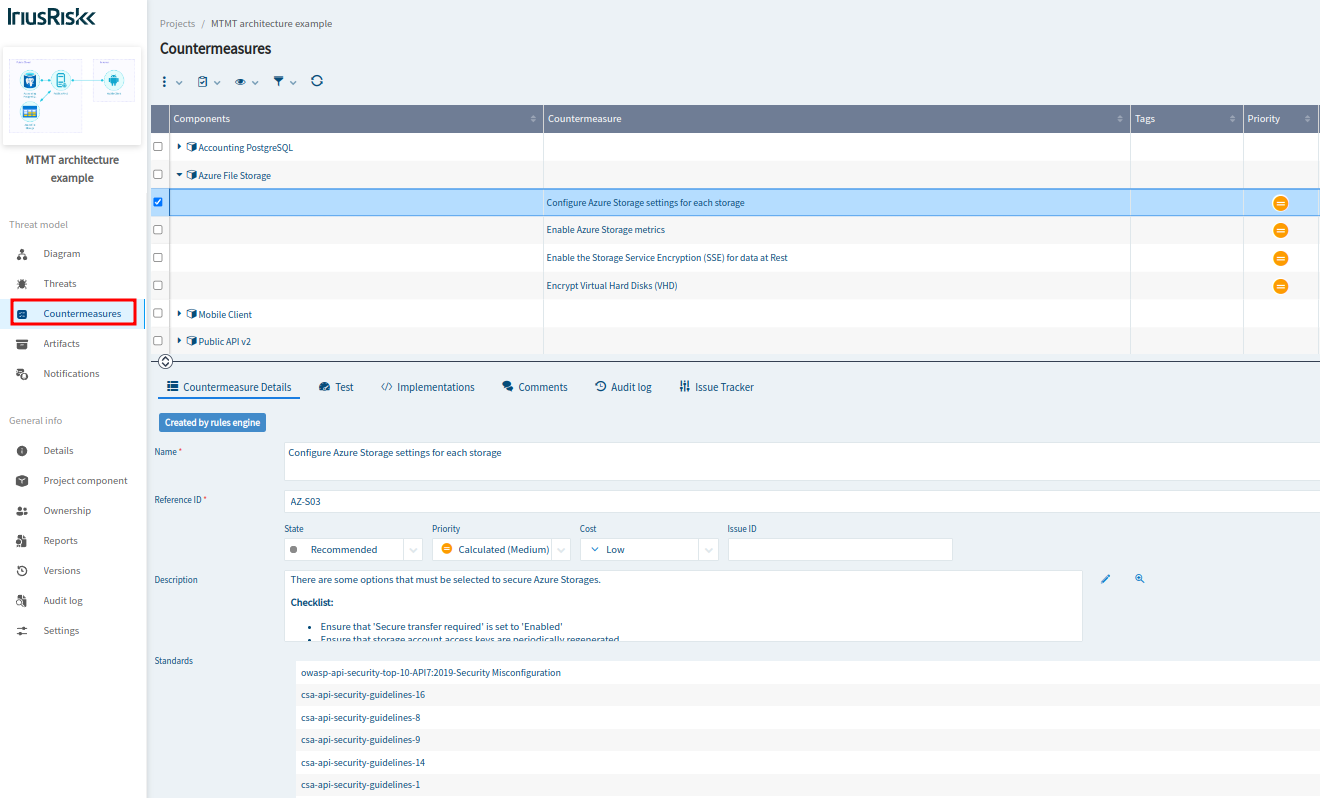
To take a look at the recommended countermeasures, you should visit the “Countermeasures” section:
Conclusion
In this step-by-step tutorial we've seen how to automatically create a threat model in IriusRisk from a simple AWS architecture designed with Visio. This could be used as a first step to create a CI/CD pipeline that automatically creates threat models for AWS architectures in the design phase, before the stack is deployed in the production environment.
References
- IriusRisk Release 4.9: https://www.iriusrisk.com/resources-blog /(future-entry-for-4.9)
- IriusRisk API Swaggerhub documentation: https://app.swaggerhub.com/apis/continuumsecurity/IriusRisk/
- IriusRisk StartLeft GitHub project: https://github.com/iriusrisk/startleft
- Microsoft Visio: https://www.microsoft.com/en-us/microsoft-365/visio/flowchart-software



